From Engagement to C3PAO Ready: A Proven Path
5-phase implementation approach completed in under 5 months, accelerating your path to independent assessment
Why Implementation Matters
CMMC (Cybersecurity Maturity Model Certification) compliance is not just a technology project. It requires aligning people, processes, and systems around a documented, auditable framework. Without a structured approach, organizations risk scope creep, evidence gaps, and extended timelines that erode the value of their compliance investment.
ITG’s SENTRE implementation methodology is built around a single principle: deliver a fully operational, audit-ready environment in the shortest time possible, with the least disruption to your ongoing business operations.
5
Months to Assessment
110
CMMC Level 2 Controls Managed
Minimal
OSC (Organization Seeking Certification) Internal Workload
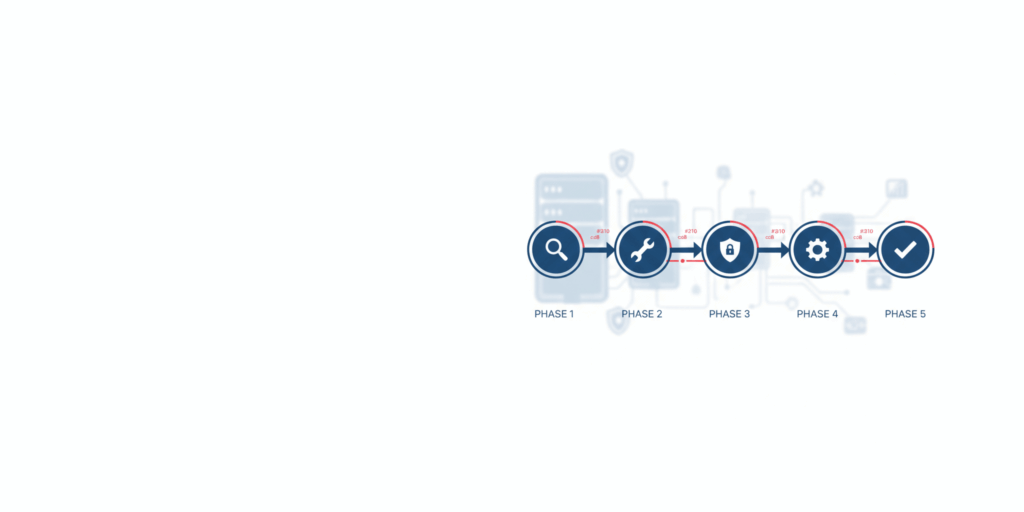
The 5-Phase Approach
1
Workflow Configuration
Tailor SENTRE workflows to your contract lifecycle
2
Users, Roles & Governance
Define users, roles, responsibilities using least-privilege principles
3
System Configuration
Configure environment, deploy hardened CUI (Controlled Unclassified Information) devices
4
Training & Monitoring
Train users, activate SENTRE as the system of records
5
Assessment Readiness
Finalize SSP (System Security Plan), achieve readiness for C3PAO (Certified Third-Party Assessment Organization) assessment
Phase 1: Workflow Configuration
Tailor SENTRE workflows to your contract lifecycle—recording awards, approving orders and delivery orders, and managing logistics and inventory. This preserves your business practices while embedding CMMC evidence collection at every step for seamless compliance.
Phase 1 Deliverables
- Contract award workflow configured
- Delivery order and purchase order workflows configured
- CLIN/SLIN structures mapped
- Logistics and inventory workflows established
- CUI data flows documented
- Workflow validation and testing completed
- User acceptance sign-off on workflows
- Workflow configuration documentation finalized
Phase 2: Users, Roles & Governance
Define users, roles, and responsibilities using least-privilege and segregation-of-duties principles. Map job functions to SENTRE roles, establish approval chains, and form a Compliance Management Review Board for governance over CMMC decisions, risks, and continuous monitoring.
Phase 2 Deliverables
- User accounts created and roles assigned
- Least-privilege access controls configured
- Segregation of duties enforced
- Approval chains established
- Compliance Management Review Board formed
- Governance charter documented
- Role-based access control validation completed
- User provisioning procedures documented
Phase 3: System Configuration & CUI Workstations
Configure the SENTRE environment, integrate with Active Directory, test end-to-end permissions for CUI access, and deploy hardened CUI laptops and workstations with endpoint protection, encryption, and secure enclave connectivity.
Phase 3 Deliverables
- SENTRE environment fully configured
- Active Directory integration completed
- End-to-end CUI access permissions tested
- CUI workstations deployed and hardened
- Endpoint protection activated
- Full-disk encryption enabled on all endpoints
- Secure enclave connectivity validated
- Baseline security configuration documented
Phase 4: Training, Utilization & Monitoring
Train users for efficient, CMMC-aligned daily operations. Activate SENTRE as the system of record for contracts, orders, incidents, and changes.
Enable system and network monitoring with logs, alerts, dashboards, and regular Compliance Board reviews.
Phase 4 Deliverables
- User training delivered to all staff
- Training materials created and documented
- SENTRE live as system of record
- System monitoring activated
- Alert rules configured
- Executive dashboards created
- Compliance Board established
- Incident response procedures validated
Phase 5: Documentation & Assessment Readiness
Finalize your System Security Plan (SSP) to match the live SENTRE environment. Organize artifacts mapped to CMMC Level 2 practices, achieving full C3PAO readiness with proven workflows, trained users, active monitoring, and complete evidence packages.
Phase 5 Deliverables
- System Security Plan (SSP) finalized
- Policies and procedures updated
- Control narratives written
- Evidence package organized
- Audit logs extracted and labeled
- Change management records compiled
- Incident records prepared
- Training records organized
- Vulnerability scan results compiled
- Configuration baselines documented
- Assessment readiness review completed
- C3PAO briefing package prepared
Key Success Factors
Clear Scope from Day One
- CUI boundary defined before configuration begins
- Non-CUI systems explicitly excluded
- Scope agreement signed by stakeholders
Minimal Disruption by Design
- Implementation runs in parallel to existing operations
- Phased rollout reduces single points of failure
- ITG assumes primary technical burden
Assessment Readiness Through Execution
- Evidence generated automatically during operations
- Documentation updated continuously, not in a last-minute sprint
- Annual internal audits validate control effectiveness
Ready to move from planning to operating in a CMMC Level 2–aligned environment? SENTRE provides a defined, auditable enclave built on ITG’s proven Federal IT capabilities.
